Cocos AI is a cutting-edge platform meticulously engineered to empower organizations and developers in executing confidential workloads within secure enclaves known as Trusted Execution Environments (TEEs). Whether operating in private, hybrid, or public cloud settings, Cocos AI excels in provisioning secure encrypted Virtual Machines (VMs).
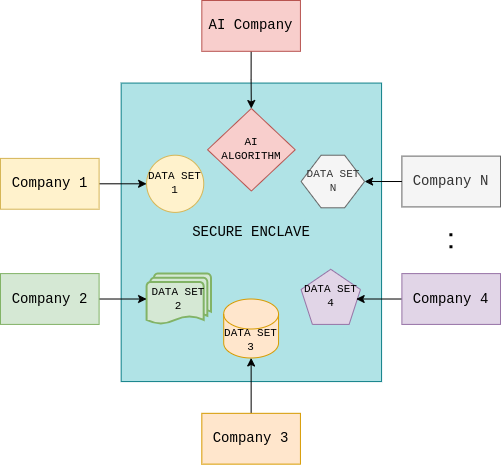
At its core, Cocos AI offers an extensive Hardware Abstraction Layer (HAL) and runtime environment within these VMs, orchestrating secure computations and vigilantly monitoring their execution. This unique combination of features sets the stage for Secure Multi-party Computation (SMPC), enabling organizations to collaborate securely on AI projects while preserving the privacy of sensitive data.
Cocos AI is more than just a platform; it's a catalyst for privacy-preserving collaborative AI. It equips users with a versatile set of tools, libraries, and software components, facilitating seamless and secure data exchange. This capability enables developers to engage in collaborative AI initiatives with confidence, knowing that their data remains confidential throughout the process.
With Cocos AI, secure data sharing becomes a reality. Organizations can harness the power of AI while ensuring the utmost privacy and security for their data. Collaborate, innovate, and harness the potential of AI in a confidential and protected environment with Cocos AI.
Cocos AI simplifies computation definition and management, enabling users to effortlessly define and execute secure workloads within Trusted Execution Environments (TEEs). This feature facilitates efficient orchestration of computations while maintaining data confidentiality.
Cocos AI empowers users with fine-grained access control through policies and attribute-based access control (ABAC) or role-based access control (RBAC). Ensure that only authorized entities access your confidential workloads and data.
Cocos AI excels in secure VM provisioning, management, and monitoring, ensuring the confidentiality and integrity of virtualized environments. Seamlessly deploy and maintain secure Virtual Machines for your workloads.
Cocos AI integrates a comprehensive Hardware Abstraction Layer (HAL) and runtime environment inside secure enclaves. This enables the execution of workloads with a focus on security and confidentiality.
Cocos AI includes an In-Enclave Agent, serving as an execution scheduler and coordinator within secure enclaves. This agent enhances the efficiency and security of your workloads.
Cocos AI ensures end-to-end encryption for traffic, safeguarding the confidentiality and integrity of data transmissions. Collaborate on AI projects with the assurance that your data remains secure.
Cocos AI implements a robust remote attestation mechanism, verifying the integrity of remote systems. This ensures that your workloads run in trusted environments, even in untrusted or remote settings.
Cocos AI offers an intuitive user interface, simplifying the management and orchestration of secure workloads. Experience seamless control over your confidential computing environment.
Cocos AI offers comprehensive platform logging and instrumentation support, including Grafana, Prometheus, and OpenTracing integration. Gain complete visibility and insight into your secure computing environment's performance.
Cocos AI facilitates container-based deployment using Docker and Kubernetes for cloud components. Additionally, it offers a set of provisioning and configuration scripts for confidential server components. Streamline your deployment process for enhanced efficiency.
Cocos AI provides a comprehensive Software Development Kit (SDK) and Command-Line Interface (CLI), simplifying development and management tasks. Accelerate your workflows and interactions with the platform.
Cocos AI boasts a small memory footprint and lightning-fast execution, ensuring optimal performance. Execute your workloads efficiently without compromising on speed.
Cocos AI adopts a domain-driven design architecture, resulting in high-quality code and comprehensive test coverage. Rely on a platform built with meticulous care and dedication to open-source excellence.
Cocos AI is open source, published under the Apache 2.0 license, enabling transparency, rapid bug fixing, customization, and collaboration. It fosters heightened security and innovation within a thriving developer community.
Explore Cocos AI:
Visit Cocos AI GitHubCocos AI, the pinnacle of secure collaborative AI, boasts an intricately designed architecture tailored to meet the complex demands of confidential computing and collaborative artificial intelligence. This architecture empowers developers and organizations with a robust foundation for secure, scalable, and innovative AI applications.

1. Cloud Services: Cocos AI leverages a microservices-based architecture, with each service containerized using Docker and orchestrated by Kubernetes. These cloud services include the Computations service, responsible for managing confidential multi-party computations deployed within secure enclaves, Users service, that offers user and organization management, Authorization service, ensuring robust authentication and policy-based authorization, and an intuitive user interface (UI).
2. TEE Manager: The Trusted Execution Environment (TEE) Manager is a critical microservice running on host hardware equipped with TEE hardware. Its role is to dynamically deploy and configure TEEs required for confidential multi-party computations. Once a computation is deployed within a newly-created TEE, the Manager actively monitors its execution and health. After the computation is complete and the result is extracted from the enclave, the Manager ensures the secure destruction of the TEE and nullifies all associated data, maintaining confidentiality.
3. In-Enclave Agent: The In-enclave Agent is an open-source, lightweight component running within the enclave. It serves as a coordinator for algorithm execution, establishing TLS-encrypted channels over which clients (Data Providers and Algorithm Providers) can securely upload AI algorithms and datasets. Additionally, the In-enclave Agent provides remote attestation for the TEE, ensuring the integrity of the execution environment.
User creates a Computation, defines characteristics, and participants. A secure VM (TEE) is provisioned and prepared for use.
Program and Data Providers upload programs and datasets into the enclave using secure CLI and remote attestation.
Programs are executed over combined datasets, coordinated by an in-enclave Agent, following the Computation manifest.
Results are sent to the Result Consumer user as the algorithm completes execution inside the enclave.
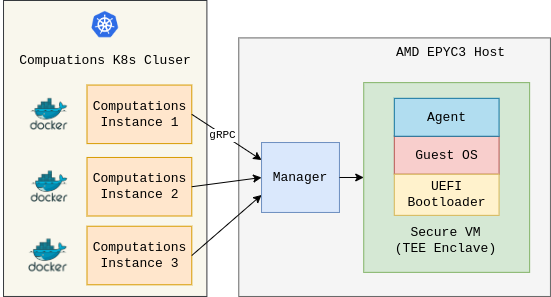
TEE Manager is a pivotal component within the Cocos AI architecture, dedicated to enabling dynamic deployment and configuration of Trusted Execution Environments (TEEs) required for confidential multi-party computations.
When a computation is initiated, TEE Manager orchestrates the creation of secure TEEs, equipping them with the necessary hardware and runtime support. It continually monitors the execution and health of each enclave, ensuring that computations run securely and efficiently.
Once a computation is completed and its result is securely extracted from the enclave, TEE Manager is responsible for the timely destruction of the used TEEs and the erasure of all related data, preserving confidentiality and data integrity.
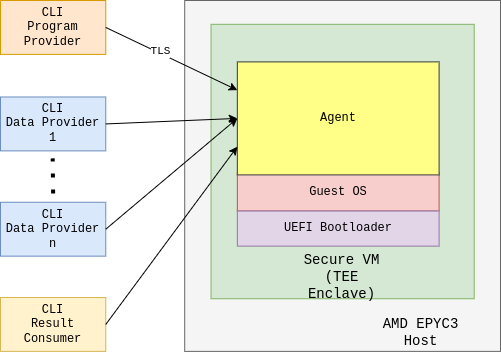
In-enclave Agent is a lightweight, open-source component at the heart of Cocos AI. Operating within secure enclaves, this agent plays a crucial role in coordinating the execution of algorithms and ensuring the secure exchange of data.
The In-enclave Agent establishes TLS-encrypted channels, allowing clients such as Data Providers and Algorithm Providers to securely upload AI algorithms and datasets. It also facilitates remote attestation for Trusted Execution Environments (TEEs), ensuring the integrity and authenticity of the execution environment.
With its capabilities, the In-enclave Agent contributes to the platform's robust security and efficient execution of AI computations, making it a key component for ensuring confidentiality and data protection.
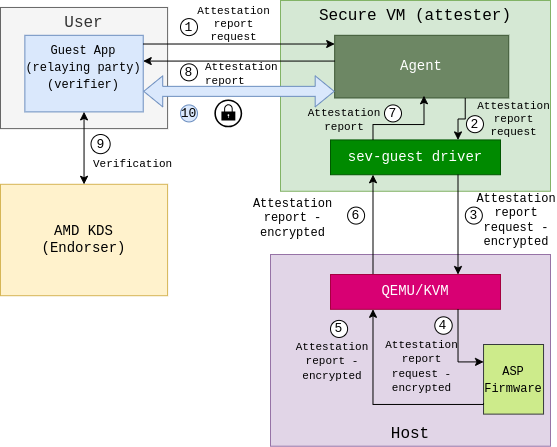
Remote Attestation is a critical component of Confidential Computing, leveraging Trusted Execution Environments (TEEs) to ensure the integrity and security of remote systems and applications. It allows you to establish trust and verify the authenticity of your computing environment, even in untrusted or remote settings.
With TEEs, remote attestation guarantees that your data and workloads run within secure enclaves, isolated from potential threats. This process involves verifying the identity of a remote system, ensuring it is running trusted and unaltered software, and encrypting data transmissions for secure communication.
By using Remote Attestation in Confidential Computing, you can confidently collaborate and process data across untrusted networks while maintaining the highest level of security and privacy.
In the healthcare sector, Cocos AI brings the power of confidential computing and secure multi-party computation (SMPC) to protect sensitive patient data and enable collaborative research. Healthcare organizations can securely share and analyze patient records, conduct research on medical data, and develop AI-driven healthcare solutions while maintaining data privacy and compliance with regulations.
In the finance sector, Cocos AI enhances data security and privacy for financial institutions and organizations. It enables secure data sharing and collaborative financial analysis while protecting sensitive financial data. Financial organizations can securely exchange financial information, perform risk assessments, and develop AI-driven financial models, all within confidential computing environments.
In government agencies and institutions, Cocos AI ensures data security and privacy for critical government operations. It enables secure multi-party computation (SMPC) for collaborative data analysis, secure data sharing between government departments, and confidential computing for sensitive government applications. Government entities can leverage Cocos AI to protect classified information, enhance cybersecurity, and drive data-driven policy decisions.